Protecting Processes with a Kernel-Level Process Protector
Is your critical process vulnerable to malicious code injection or termination? The "Rhydon1337/windows-kernel-process-protector" project offers a novel approach to safeguarding specific processes within the Windows kernel, but its implementation requires understanding the risks and benefits of kernel-level modifications.
- Understanding the Problem: Kernel-Level Protection
- The Process Protector Approach: A Targeted Kernel Patch
- Bypassing Security Restrictions and Validation
- Implementation and Key Steps
- Benefits and Considerations
- Alternative Techniques: DLL Injection and Detours
- Process Protection Technologies, LLC (PPT)
-
Rhydon1337/windows-kernel-process-protector FAQ
- What is the Rhydon1337/windows-kernel-process-protector project designed to do?
- Why does the project use a kernel patch?
- How does the kernel patch work?
- What are the installation steps?
- What are the potential risks of modifying the kernel?
- How does the project protect processes beyond direct kernel modification?
- Is this project suitable for production environments?
- What is the role of the "testing mode" in the project?
- What is the relationship between this project and Process Protection Technologies, LLC (PPT)?
Understanding the Problem: Kernel-Level Protection
Protecting a process effectively requires a deep understanding of the operating system's kernel and how it manages processes. The kernel is the core of the operating system, responsible for managing hardware resources and all running processes. Any attempt to modify or inject malicious code into a process often requires accessing the kernel. So, a robust solution like the "Rhydon1337/windows-kernel-process-protector" project is crucial. This project demonstrates a sophisticated approach to process protection by employing techniques that interact directly with the kernel-level processes.
The fundamental challenge with kernel-level process protection lies in security considerations. The system must protect itself from unauthorized modifications, and this protection often includes digital signatures for kernel-mode drivers. These signatures ensure that loaded drivers haven't been tampered with or replaced by malicious actors.
The Process Protector Approach: A Targeted Kernel Patch
The "Rhydon1337/windows-kernel-process-protector" project cleverly addresses this security issue by using a targeted kernel patch. Instead of universally disabling security checks, the patch focuses on a specific driver and is only active in testing environments.
This targeted approach avoids the risks associated with disabling critical system integrity checks. A wide-ranging approach like that could compromise the system's stability and security for all processes. This project's strategy is a delicate balance between providing needed protection and ensuring the overall health of the system. The patch modifies a specific flag within the kernel's internal data structures, specifically manipulating the LDRP_VALID_SECTION flag in the PKLDR_DATA_TABLE_ENTRY structure, effectively allowing the kernel to consider the process protector driver as valid even if it's not digitally signed. This is done carefully and selectively.
This process protector allows for the loading of the driver without requiring a system-wide compromise. The use of a "testing mode" flag ensures that this critical operation doesn't introduce vulnerabilities into production environments.
Bypassing Security Restrictions and Validation
The core innovation lies in overriding the kernel's signature validation for the specific driver. This controlled modification allows the process protector driver to load and function without needing a forced bypass of system-wide security. This targeted approach is a significant improvement over more aggressive methods. This level of control and specificity is key to minimizing potential risks and ensuring stability.
The solution is specifically designed to avoid disabling fundamental integrity checks, which is critical for maintaining system security. By patching the validation process for the specific process protector driver, the system maintains its overall security posture while enabling the necessary protection for designated processes. The success of this approach hinges on meticulous testing and a very narrow scope of alteration.
Implementation and Key Steps
The installation and operation of the process protector follow a well-defined sequence:
- Installation: The driver is installed using the standard Windows service manager.
- Start: The service is started, allowing the process protector to load into memory.
- Process Protection: The
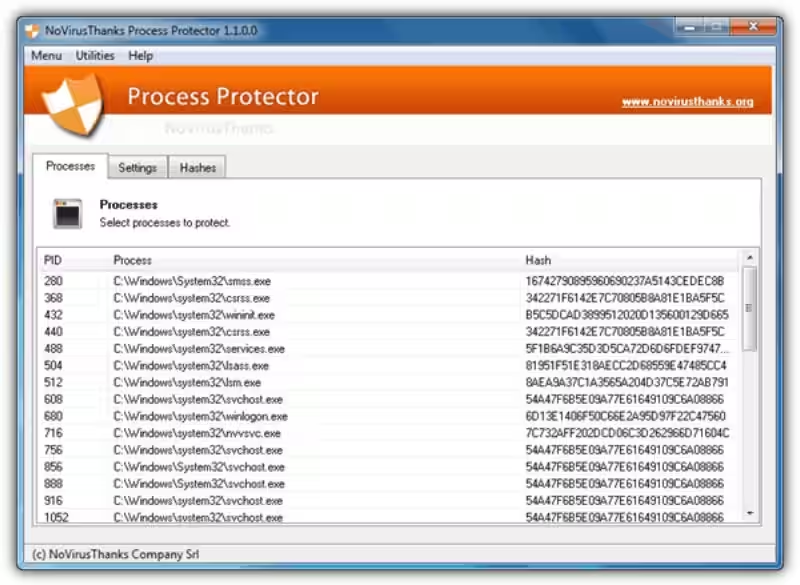
ProcessProtectCommander.exeapplication is utilized to specify the target process's PID (Process Identifier). This trigger activates the process protection mechanism within the loaded driver.
This straightforward process allows administrators to deploy the process protector and target its protection capabilities at specific processes.
Benefits and Considerations
The core benefit of this approach is targeted process protection without compromising the integrity of the entire system. The controlled modification of the kernel's internal structures through patching ensures that the process protector can function without compromising crucial system integrity checks. This method is a significant advancement over broader approaches.
However, modifying the kernel's internal structures introduces security risks. Extensive testing and rigorous documentation are paramount to avoid unintended consequences or vulnerabilities. The code must be robust and well-maintained to mitigate potential issues. The process protector must be used cautiously and only after careful evaluation of the risks versus benefits.
Alternative Techniques: DLL Injection and Detours
The project leverages additional techniques for greater control and flexibility.
DLL injection and hooking (interception of system functions) via tools like Microsoft Detours are vital for intercepting crucial system functions such as NtQuerySystemInformation and NtOpenProcess. This helps to grant the process protector access to information about running processes and their actions without requiring administrative privileges in all situations. A helper library, HookLib or ProcessUtils, simplifies these actions, allowing for easier and more structured implementation of these crucial interceptions. The utilization of these supporting libraries allows the core logic of the process protector to be more streamlined and maintainable.
Process Protection Technologies, LLC (PPT)
Process Protection Technologies, LLC (PPT), while not directly involved in the development of the process protector, highlights the importance of process protection in various industrial settings. Their expertise in providing equipment and technologies for manufacturing and processing sectors underscores the need for solutions that protect critical processes from interference and maintain the integrity of manufacturing output.
PPT's portfolio encompasses magnetic separation, metal detection, and X-ray inspection systems, all aimed at ensuring the quality and safety of manufactured products. They also provide material handling equipment for the efficient and safe movement of materials throughout the manufacturing process. Their offerings demonstrate the wide-ranging applications of process protection technologies beyond the digital realm.
In conclusion, the "Rhydon1337/windows-kernel-process-protector" project represents a significant advancement in process protection, offering a targeted approach to kernel-level intervention. While carrying inherent risks, the project's meticulous design and controlled execution demonstrate a potential solution for safeguarding critical processes within the Windows environment. The core principle of the process protector, providing a controlled and robust approach to protection of vital processes, is a valuable approach in numerous fields.
Rhydon1337/windows-kernel-process-protector FAQ
What is the Rhydon1337/windows-kernel-process-protector project designed to do?
The project aims to protect a specified process running on Windows from malicious code injection, termination, and hooking attempts within the kernel. This protection is achieved by leveraging the Windows Object Manager's callback routines.
Why does the project use a kernel patch?
The initial approach using callback routines faced a critical issue: STATUS_ACCESS_DENIED errors. These errors arose because the callback routines weren't in a digitally signed kernel-mode driver binary. Using a kernel patch, the project modifies the kernel's driver loading mechanism to accept the unsigned driver, addressing the security check without disabling system-wide integrity checks.
How does the kernel patch work?
The patch targets the LDRP_VALID_SECTION flag within the PKLDR_DATA_TABLE_ENTRY structure for the driver. By modifying this flag, the kernel is effectively told that the driver is valid, even if it lacks a digital signature. Critically, this modification is only applied when the system is in testing mode.
What are the installation steps?
- Install the driver using the standard Windows service manager (
sc create ...). - Start the service (
sc start). - Use the
ProcessProtectCommander.exeapplication to specify the target process's PID to trigger process protection.
What are the potential risks of modifying the kernel?
Modifying the kernel's internal structures carries security risks. Thorough testing is essential to mitigate potential unintended consequences or exploitable vulnerabilities. The code needs to be robust and well-documented.
How does the project protect processes beyond direct kernel modification?
The project also employs techniques like Microsoft Detours, DLL injection, and hooks to intercept system functions like NtQuerySystemInformation and NtOpenProcess. A helper library (HookLib, ProcessUtils) simplifies these implementations.
Is this project suitable for production environments?
No, the kernel patch is designed for testing environments only. Production environments should maintain standard driver signature validation to avoid security risks.
What is the role of the "testing mode" in the project?
The "testing mode" configuration is crucial for limiting the impact of the kernel patch. It ensures that the driver signature validation bypass is only active during testing, preventing unintended consequences in production systems.
What is the relationship between this project and Process Protection Technologies, LLC (PPT)?
Process Protection Technologies, LLC (PPT) is a separate company specializing in manufacturing and processing equipment, with expertise in magnetic separation, metal detection, X-ray inspection, and material handling. The two entities are not directly related regarding this project.
